Featured
- Get link
- X
- Other Apps
Rabbitmq Jwt Authentication
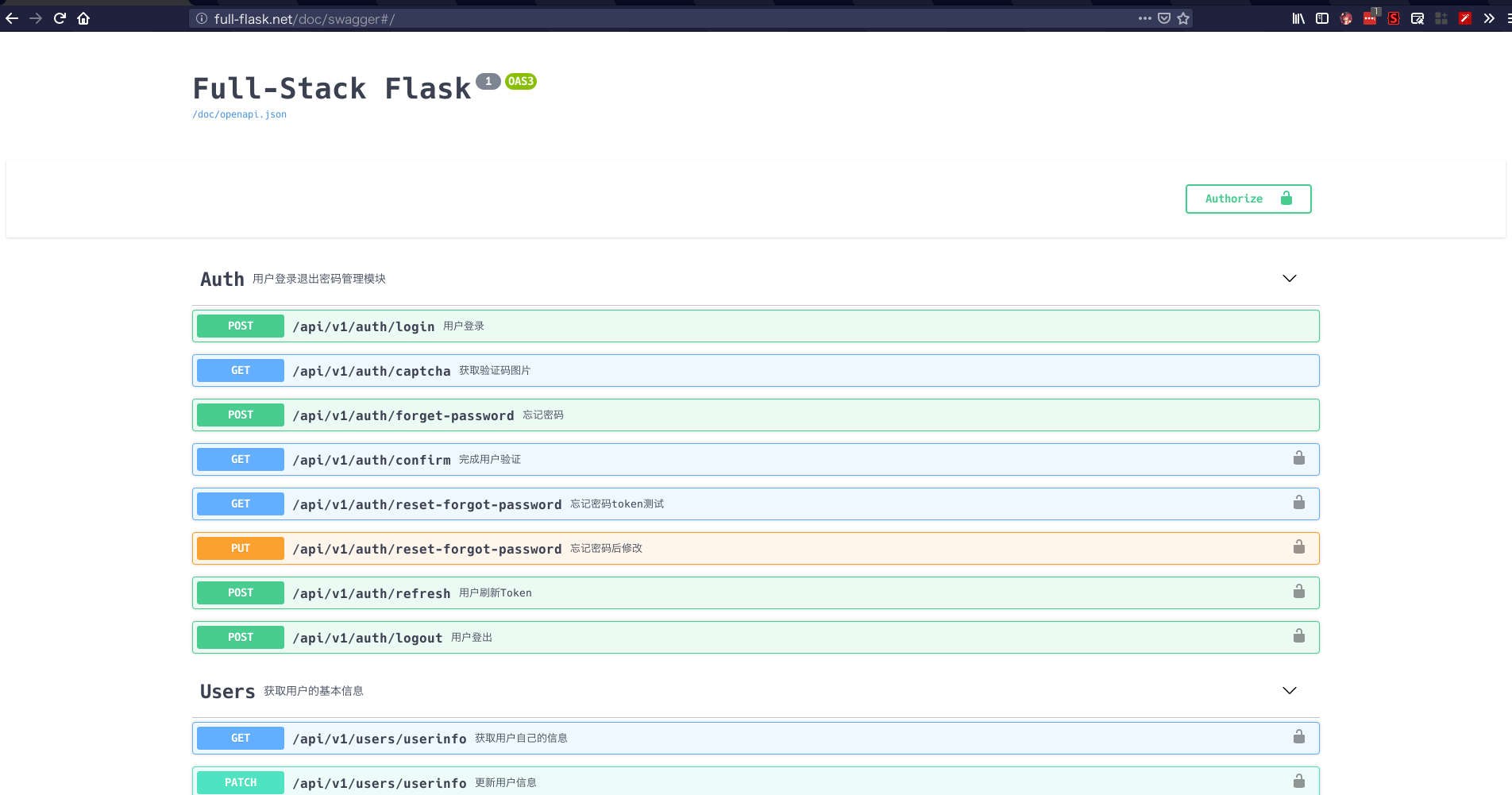
Rabbitmq Jwt Authentication. Next, we will implement an api route that can be accessed only with the help of a valid jwt. Mlflow app using react, hooks, rabbitmq, fastapi server, celery, microservices 08 december 2021.
The refresh token lives a little bit longer (expires in 24 hours, also customizable). This plugin aims to provide oauth 2.0 authorization for rabbitmq clients. The jwt is acquired by exchanging an username + password for an access token and an refresh token.
You Will Have To Wait Until 3.8 Is Released.
It is comparable to an authentication session. We're trying to set up rabbitmq to authenticate services using jwt service account tokens (provisioned by an internal service). Oauth enables developers to access the rabbitmq management ui using their tas for vms credentials instead of using the binding credentials from a service key.
Authentication And Authorization Are Managed By Rabbitmq (Vhost, Account, Etc.) ==> Once Again, All User Related Data Are Lost.
In practical terms this means that on the client side, a jwt token has to be provided in the password field. Ardaorkin1 june 14, 2021, 6:19am #1. The scope format recognized by rabbitmq is as follows
The Refresh Token Lives A Little Bit Longer (Expires In 24 Hours, Also Customizable).
Customers sign in by submitting their credentials to the provider. Moreover, we have 2 repositories to manage authentication and authorization. If you want to make a proper logout, you'll need to use oauth2.
I Have Private Key From Azure Adb2C User Flow Generated Metadata Document Jwks Uri.
Next, we will implement an api route that can be accessed only with the help of a valid jwt. There are three such mechanisms built into the server: Let the users authenticate with a username/password.
This Plugin Must Be Compiled Against The Unreleased Version 3.8 Of Rabbitmq.
For this we will update advanced.config file with following details {rabbitmq_auth. Jwt is a token that can be used as part of the oauth authorization protocol. Authentication mechanisms are now documented in the access control guide.
Comments
Post a Comment